Detect intrusions in minutes, not months.
Trapster deploys decoys (fake servers, credentials and files) on your network. As soon as an attacker touches one, you receive an instant and reliable alert. No configuration, no false positives, no SOC fatigue.
Designed by offensive security experts
Your SOC is drowning in alerts, maybe.
EDR, SIEM and XDR generate oceans of signals. Analysts spend their days proving what is not a threat. Real intrusions get lost in the noise.
From deployment to detection in four steps.
Download
pre-configured VMs and adapted to each enterprise
Installation
on the network (VMWare, Hyper-V or Proxmox)
Configuration
with a pre-configured template or a wide selection of services (HTTP, FTP, SSH, SMB, DNS, LDAP, etc.)
Monitoring
Your trapsters monitor your network while you work
Reception
of an alert by email and notification on the dashboard
Analysis
of the alert
Login
with your other security tools to eliminate the threat
Deploy your decoys
Fake servers, databases, credentials and files, indistinguishable from your real systems. Deploy in any subnet in minutes (VMware, Hyper-V, Proxmox, etc.).
Stay silent
Decoys are invisible to legitimate users, they have no reason to be touched. Zero legitimate traffic = zero false positives. Your trapsters monitor while you work.
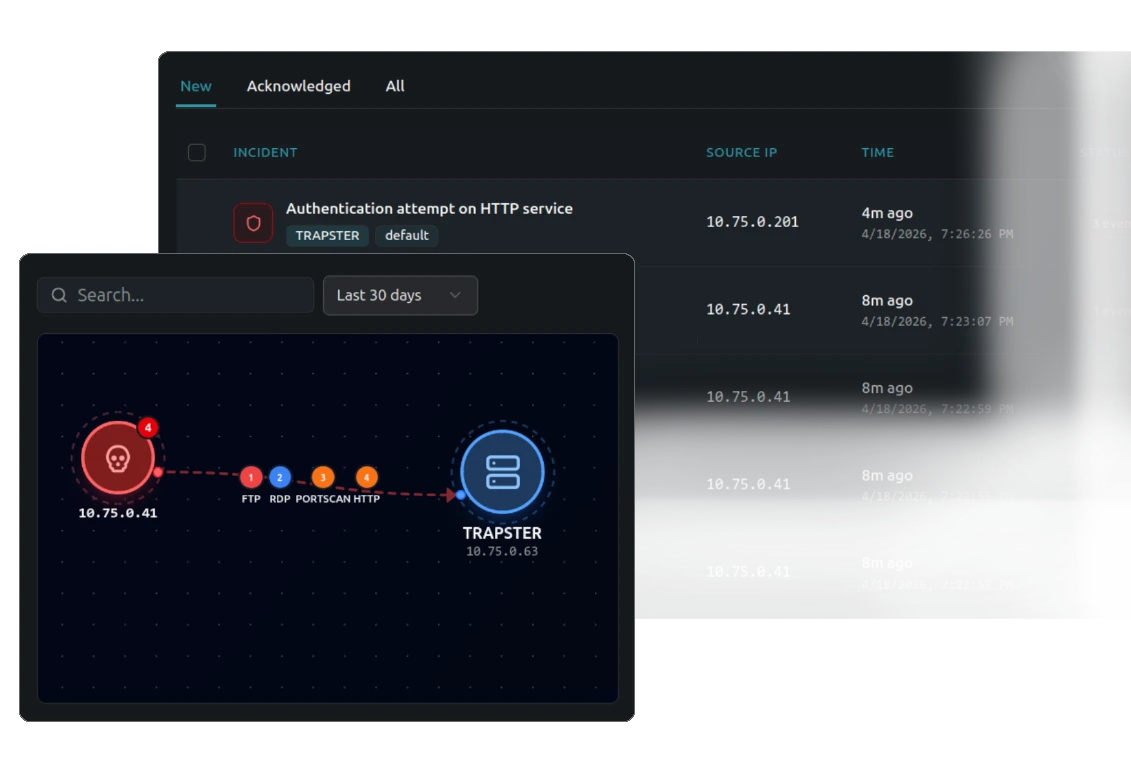
Detect at first contact
As soon as a decoy is probed, scanned or authenticated, an attacker is inside. High-confidence alert with full session capture, sent by email, Slack, Teams or dashboard.
Respond with evidence
Every keystroke, every command, every payload recorded. Connect directly to Sekoia, Splunk or your SOAR via Syslog or our API REST.
Everything a deception program requires. Nothing more.
Designed for analysts who don't have time to learn a new tool. Ten minutes for the first decoy. Ten seconds for the first alert.
Fast installation
Deployment in minutes, automatic configuration
Easy to use
No advanced technical skills required
Few false positives
High-fidelity alerts, targeted investigation
French Cloud
Hosted on OVHCloud, developed in France
Honeytokens
Trapped credentials, fake API keys, decoy files, any interaction triggers an instant alert
Action capture
Every piece of data, command, and payload recorded

ISO 27001 Certified
Certified by BSI Group, ensuring the confidentiality, integrity and availability of your data.
Let attackers find you first.
30 minutes. One call. We map decoys on your network and show you what an attacker would see, before they do.
A product of Ballpoint

Designed by offensive security experts
Our finding after hundreds of penetration tests: too few companies detect attacks in time. EDR/XDR solutions are often bypassed by experienced attackers.
Trapster was born from this field reality. As pentesters, we know that a well-placed honeypot is one of the most effective tools for detecting an intrusion.